Currently, since March 2018, SSL/TLS certificates (more commonly called HTTPS certificate) can have a maximum lifetime of 825 days.
But in March 2020, Apple announced that they only will allow SSL/TLS certificates on Safari that have a maximum validity of 398 days (13 months). And Google will follow this path (announced by the chair emeritus of CA/B Forum on Twitter in June 2020).
In July, Mozilla has confirmed it will reduce certificate lifespans too.
This will apply from September 1, 2020, for all certificates (DV, OV, EV). Certificates that were issued prior to this date will not be affected and will be valid until the end of their validity date.
Any website with a certificate issued after September 1 and with a validity lifetime longer than 13 months will be rejected by Safari, Chrome and Mozilla, and a ‘Privacy Warning’ message will be shown to users.
What does an SSL/TLS certificate bring?
HTTPS is an internet communication protocol enabling an encrypted connection between the browser and the website, which means that the exchanges are not in clear.
This allows
- Data confidentiality: in case of eavesdropping or traffic interception, data exchanged cannot be read,
- Data integrity: data can’t be modified “along the way” between being sent by the website and being displayed on the user’s browser,
- And to authenticate the website, so that the user can verify that he is on the site he wanted to go to.
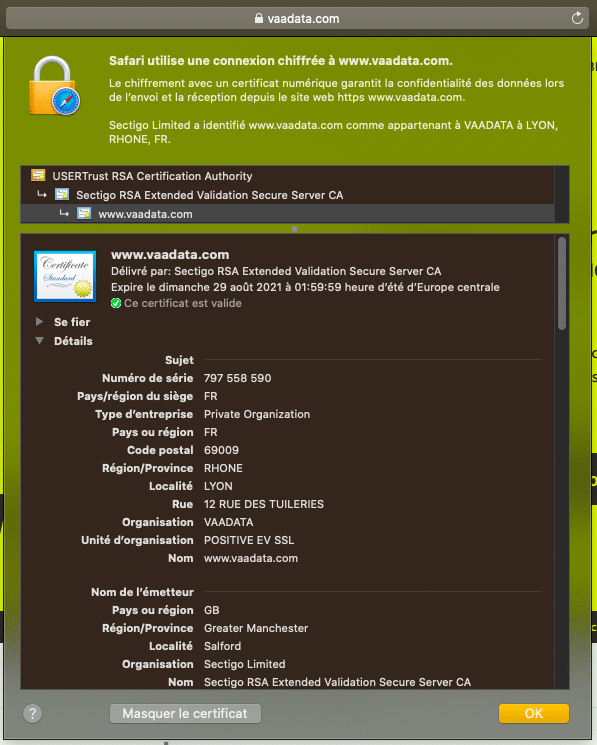
For example, if you want to verify that you are on the website www.vaadata.com, you can click on the padlock in the address bar and details will be shown on the SSL/TLS certificate.
HTTPS protects therefore from attacks where the traffic is intercepted, modified (Man-In-The-Middle attack, interception of sensitive data…).
Why moving to a shorter validity period?
Long lifetime certificates have the advantage to be renewed less often; however they present some risks
- in case of a security incident, even if a certificate is revoked, the browser might not warn about the non-validity of the certificate, as processes to verify certificates by browsers have limits.
- Indeed, browsers have two methods to verify that a certificate has been revoked: consulting Certificate Revocation Lists (CRL) or the Online Certificate Status Protocol (OCSP).
The main concerns with CRL files are that they are not updated frequently enough, that they can become large, and different sources need to be consulted.
The OCSP protocol can be relatively slow and browsers will abandon the verification request if the response time is too long. To go further regarding concerns related to revocation, we recommend you this article.
- Indeed, browsers have two methods to verify that a certificate has been revoked: consulting Certificate Revocation Lists (CRL) or the Online Certificate Status Protocol (OCSP).
- as the renewal is not frequent, this might lead to human errors (deadline forgotten, difficulties or errors in the renewal process…)
Short lifetime certificates are improving the global security as
- They reduce the window of exposure if the security of a certificate has been compromised,
- They enable to adopt the latest cryptographic norms for certificate signature faster. For example, if an algorithm is declared no longer secure enough to be used (due to changes in computer power, etc.), the renewal of certificate guarantees that in a short period of time, no one will use this algorithm again
- They encourage automation for the renewal, which should decrease human errors
In the last few years, the CA/Browser Forum, the consortium of certificate authorities and browser publishers, has gradually shortened the validity period of SSL/TLS certificates, from 10 years in the 2000s to 2 years now.
In February 2017, a proposal was put to the vote to reduce the validity period of certificates to 398 days. But the vote was against the proposal.
Apple announced alone in February 2020 the move to a shorter validity. Google and Mozilla then declared they will be reducing certificate lifespans too.
In order not to lose users, the majority of websites will use certificates with a maximum validity of 13 months.
Edit 31.08.2020: Modified to include Mozilla’s decision to reduce the maximum lifetime.