During a web application penetration test, we came across the following situation:

Multifactor authentication (MFA) is a central and widely used mechanism for strengthening the security of user accounts and access to a system.
Indeed, it is an authentication method that prevents many malicious attacks and exploits aimed at compromising data: brute force, session hijacking, privilege escalation, etc.
Pseudonymisation is a data protection technique, which consists of processing data in such a way that it is not possible to attribute them to a specific person without the use of additional information. More specifically, it involves replacing real personal identifiers ( last names, first names, emails, addresses, telephone numbers, etc.) with pseudonyms.
IDORs (Insecure Direct Object References) are widespread vulnerabilities in web applications in the same way as XSS or SQL injections. Affiliated with broken access control, IDOR vulnerabilities are indeed among those we most commonly discover and exploit during our web application penetration tests.
Principles, attack scenarios and exploits, we present in this article an overview of IDORs, as well as the best security practices and rights control tests to be carried out to prevent the risks.

Privilege escalation is a key concept for attackers seeking access to sensitive information or restricted functionality on an information system. Typically, this involves exploiting security weaknesses in a given system to escalate from a limited level of access, with standard permissions, to a higher level of access, with greater rights.
On Linux, there are several techniques for escalating a user’s privileges. Exploitation of configuration weaknesses, vulnerabilities in programs and broken access control are the main ones.
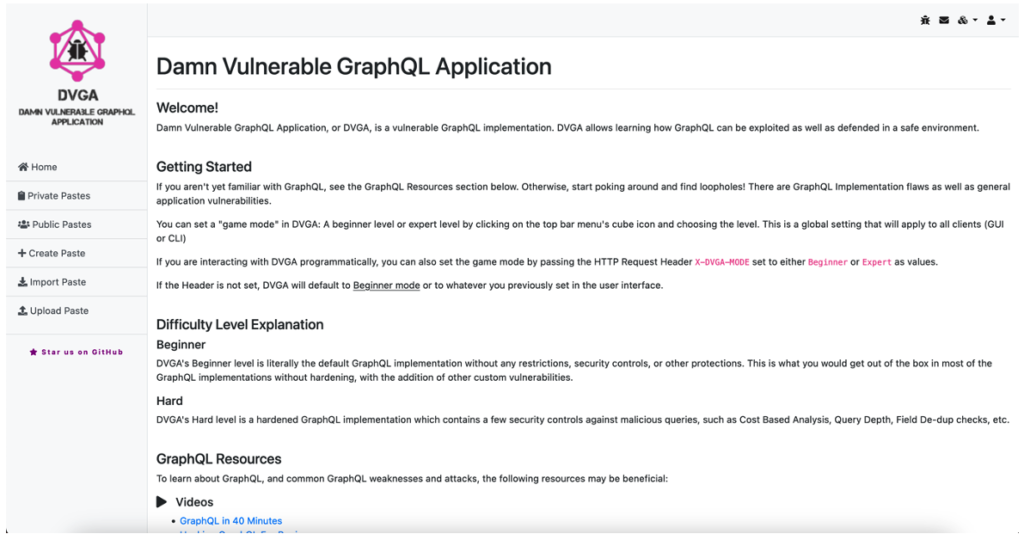
During a web application penetration test, we discovered a vulnerability related to the configuration and mismanagement of access controls on GraphQL.
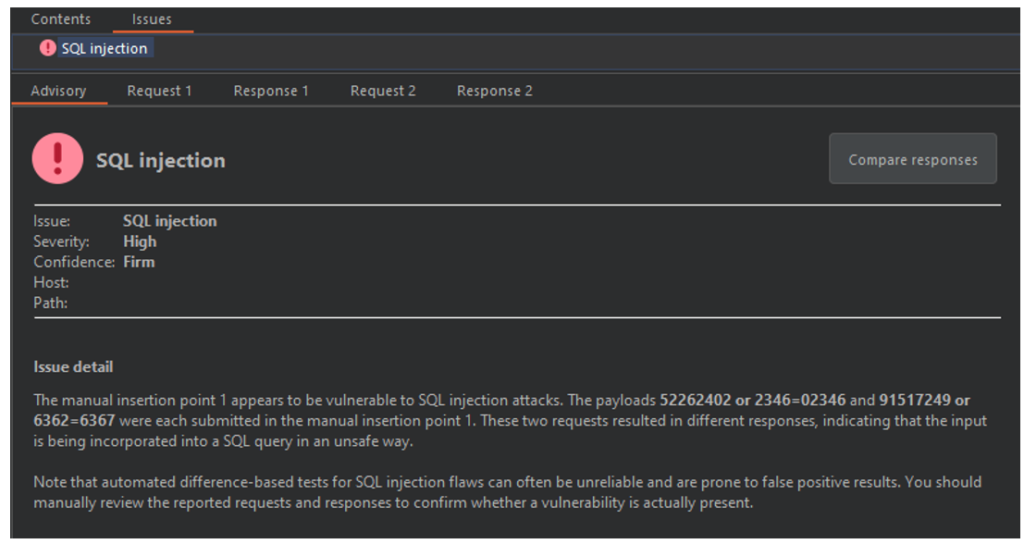
In 2021, the OWASP top 10, which highlights the most common vulnerabilities in applications, has slightly changed. Injection vulnerabilities, previously the most critical, are now in third place.
One reason for this is that developers are becoming more aware of the risks associated with injection vulnerabilities through the implementation of more secure application development tools and practices. And of course, the most important measure to mitigate the risk of SQL injection is the use of prepared statements.
This is usually done using an ORM, which can introduce new risks as we will see in this article.

When developing a game, you may need to save a player’s run to a file so that you don’t lose their progress and they can return to where they left off. Similarly, when developing an online text editor, you may want to preserve the content that the user has written.
Indeed, there are many cases where we want to save the state of our application to restore it in the future. Two terms are used to define this process: serialization and deserialization.
During our penetration tests on web platforms, one of the main attack vectors we use most often to discover and exploit vulnerabilities is rate limiting.
Based on this principle, we believe that any web application will, sooner or later, be confronted with a traffic-generating attack. These can take several forms, but the main ones are the following:

Deep links are predefined URIs (Uniform Resource Identifiers) that allow direct access to an activity in a web or mobile application when clicked.
These links are usually found on pages within a web application or in the webviews of a mobile application. When the user clicks on a deep link, and has the application to open that type of link, a popup suggests opening the link with the corresponding application.
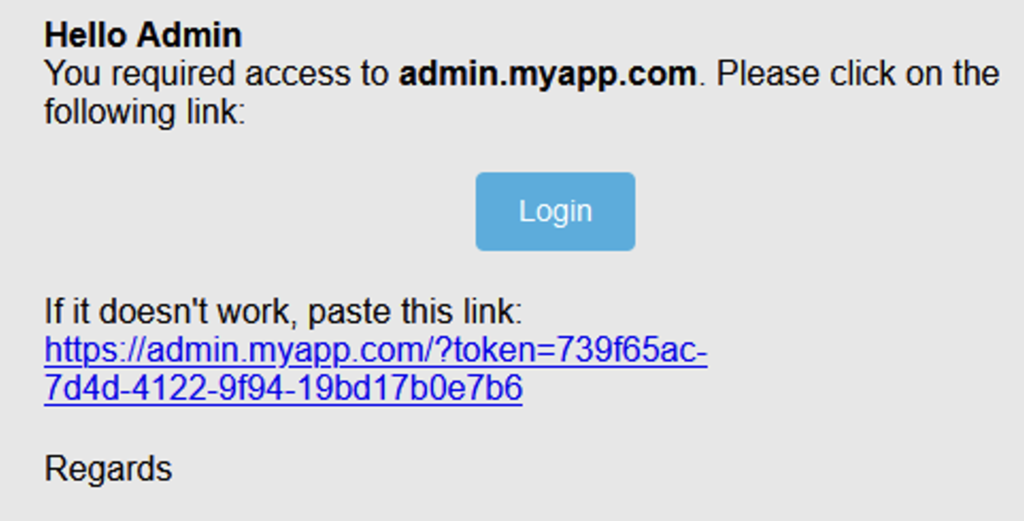
During a penetration test, we came across this situation:

Brute force is certainly one of the most trivial attack techniques. The main reason: the human factor remains the weakest link in the cybersecurity chain. Indeed, there is no need to carry out social engineering attacks or sophisticated SQL injection attacks to steal credentials because habits die hard: users’ passwords remain weak and therefore easy to guess. With the right tools, even the most novice attackers can compromise data and cripple the systems of large companies.
XSS (Cross-site Scripting) are particularly widespread vulnerabilities in web applications. In fact, more than one in two applications contains it according to various studies, both old and new. To support this statement, it is the most common vulnerability that we discover and exploit during our penetration tests on all types of applications and websites.
Principles, types of XSS attacks, exploitations, we present in this article an overview of XSS, as well as security best practices and measures to implement to counter the risks of attack.