
You will no doubt be familiar with phishing, which consists of sending malicious emails to encourage people to perform sensitive actions, such as entering their credentials on a fake authentication page.
Smishing is very similar, except that the attacker does not send emails, but text messages, hence the name smishing. Essentially, smishing is nothing more and nothing less than SMS phishing.
Broadly speaking, smishing is a social engineering technique which uses a pretext to influence its victims and push them into action, via the SMS channel. In addition, phishing by SMS or email can be used for “mass” scams or more targeted attacks, as we will see later.
Before going into detail about a concrete example of a grey box smishing campaign carried out as part of a social engineering penetration test, let’s take a look at some of the factors that need to be taken into account when identifying a malicious SMS.
In the majority of Smishing attacks, the sender’s phone number is completely unknown to the recipient, which should be enough to set off alarm bells.
The telephone code – for example +33 for France, +1 for the United States and Canada, or +258 for Mozambique – may be more or less suspect.
To give text messages more weight, the attacker can try to spoof a number familiar to the victim. For example, there are platforms for sending SMS messages or even placing calls from a virtual number. The attacker can then choose the number before launching the attack.
It goes without saying that a text message is already more credible if it appears to come from a local number – i.e. one that is geographically close to us, in the same country or even the same town. With a bit of luck, the attacker can even spoof a number that is close to one known by his victim – with only a few digits difference.
Spoofing a familiar brand is another interesting alternative for attackers. It is common, for example, to receive a legitimate SMS from one’s own bank with the name of the organisation displayed instead of a phone number.
The attacker may also choose to send the SMS using a name rather than a traditional number. Depending on the nationality of the recipients, certain restrictions may apply, in particular certain names may be reserved in certain countries to prevent them from being spoofed. Spoiler alert: this is not the case everywhere!
Key points to remember:
In short, the identity of the sender – be it a brand name or a phone number – should not be the sole criterion for determining whether an SMS is legitimate or not.
As well as the identity of the sender, which is naturally the first thing we look out for when we receive an SMS, there are certain clues in the body of the message itself that should warn us.
The notion of pretext is not specific to smishing, but is a crucial element of any social engineering attempt, as it is what incites the victim to perform the sensitive action desired by the attacker.
For example, in a targeted attack aimed at a company’s employees, the attacker might use a VPN update as a pretext to get them to enter their credentials on a fake authentication page under his control.
To achieve its objective and spur users into action, the pretext must use various psychological levers to deceive their vigilance. It is often based on a sense of urgency (e.g. “please update within 48 hours or your account will be deactivated”), curiosity (“so-and-so has just shared the following folder with you”), familiarity (especially if the attacker impersonates a familiar sender), or even authority (if the presumed sender happens to be the company’s manager or IT department).
In the case of smishing, the attacker delivers his pretext by sending an SMS to his victims. The content of the message itself contains the request, which constitutes the essential part of the pretext, but other elements also play a part in the development of a good pretext (for example, the identity of the sender, the period during which the SMS is sent, etc.).
Whether the attacker is distributing malware via an online platform or stealing login credentials, he will usually include at least one link to a domain under his control in the body of the SMS. However well-crafted the pretext, analysing this link properly – which takes a few minutes at most – can make all the difference.
To analyse a link, you first need to understand the concept of a domain name and the different levels that make it up.
Take, for example, the (legitimate) sub-domain login.microsoftonline.com. It breaks down as follows:
As we have already said, a phishing link (most of the time) points to a malicious domain – i.e. a domain that is not the legitimate one (e.g. oultook.com instead of outlook.com).
As well as inverting, replacing or omitting characters in the legitimate domain name (a technique known as “typosquatting”), attackers use a number of other tricks to fly under the radar.
In the same spirit, “combosquatting” is the combination of a keyword and the legitimate domain (for example accounts–google.com instead of accounts.google.com). Changing the TLD is another possibility (e.g. gmail.co instead of gmail.com).
In all cases, you need to check whether the domain name (in the sense of “TLD + 1”) is legitimate or not. Here’s a quick test: what do you think of paypal.securelogin.com, for example?
Key points to remember:
Now that we’ve looked at the clues you need to look out for to identify a smishing attempt, we’re going to put them into practice with an attack scenario, inspired by one of our audits.
In this example, we will be in a “grey box” condition, i.e. the business phone numbers of the employees to be targeted will have been provided to us by our customer, Koogivi.
It should be noted that in a “black box” condition – i.e. in the conditions of an external attacker with no information about the company – the search for the numbers to be targeted requires a more or less lengthy intermediate stage, as the numbers could potentially be divulged in several ways.
If an online platform is hacked, for example – which happens frequently – it is not uncommon to find contact information (including mobile numbers) in leaked data made public or sold on the dark web. More simply, LinkedIn profiles or email signatures can contain this type of information.
The reconnaissance phase is an important first step in our audits and, more generally, in any cyberattack, because it enables us to make an inventory of a company’s exposed assets and identify the most critical ones. It can also identify certain external services that are also potential entry points.
For example, let’s suppose that during our reconnaissance phase, we notice that Koogivi uses Gandi as its mail server (information revealed by MX records, for example). The webmail authentication page is as follows:
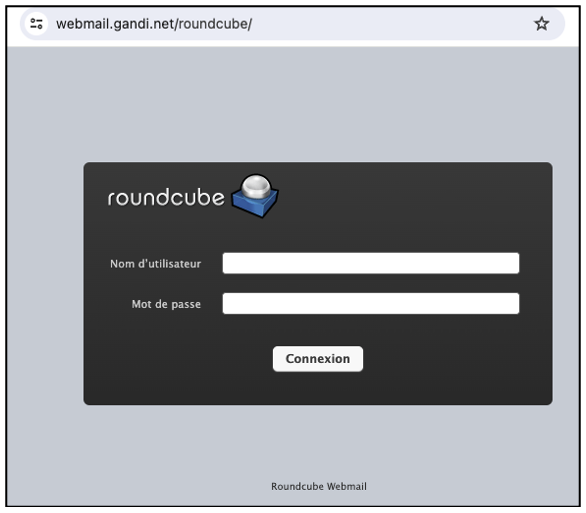
It goes without saying that webmail is an interesting point of entry for an attacker, as accessing it allows them to get their hands on potentially sensitive information – not to mention the fact that webmail passwords can give access to other internal (or external) platforms if they are re-used elsewhere.
Once the target platform has been identified, the next step is to clone the authentication page. We won’t go into (too much) technical detail on this one, but you should be aware that certain techniques allow attackers to get their victims to interact not with a classic clone, but with the real application, thus bypassing most 2 factor authentication methods.
The idea is for the attacker to place himself in the middle of the interaction between his victim and the legitimate application (in short, in a man in the middle position), as shown in the diagram below:
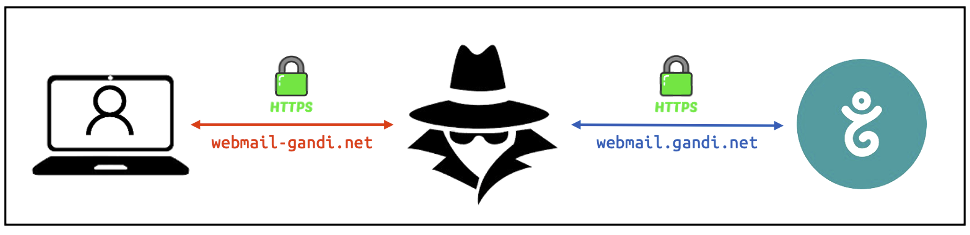
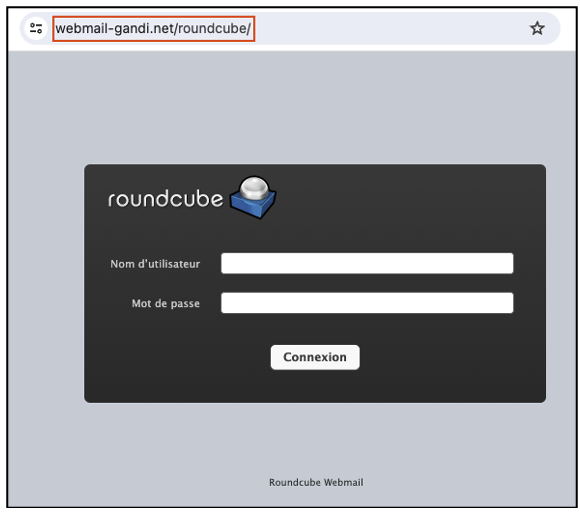
As you will have noticed, the malicious (“combosquatted”) domain we have chosen is webmail-gandi.net, which spoofs the legitimate webmail.gandi.net subdomain that hosts the legitimate authentication page. By proxying traffic between the victim and the legitimate application, the attacker can retrieve login credentials, including 2 factor authentication codes if any.
Once the malicious server has been configured, the fake login page looks like this:
And that’s it! All that’s left is to send the SMS messages using a relevant and convincing pretext to encourage the recipients to connect to the fake webmail.
Combining everything we’ve just seen, here’s what the attack could look like:
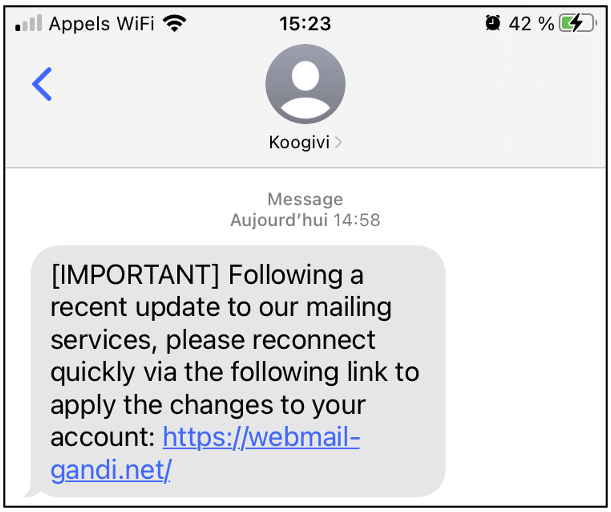
The result is quite realistic, but let’s not be too quick to fall for it, and let’s take a look at the few clues we mentioned in this article:
Finally, let’s summarise the anti-*ishing hygiene rules we’ve just seen.
A quick aside: why “*-ishing”? Because the best practices that follow are applicable to all social engineering vectors – whether phishing by email, SMS (or more precisely smishing), Teams or post (and I could go on).
Generally speaking, our recommendations cover two main areas: awareness-raising and technical measures.
Let’s start with the right reflexes that all employees should be aware of. First of all, to identify smishing attacks, you need to systematically take the time to analyse the key clues:
To err is human, and all it takes for the attack to succeed is for the pretext to resonate with what the recipient expects or is in the process of doing. You may not believe me, but anyone can be fooled, and I would go even further: adopting this mindset is one of the surest ways of remaining vigilant and not erring on the side of overconfidence. In any case, you also need to make your employees aware of the right reflexes to adopt in the event of an attack:
Now that we’ve looked at awareness-raising measures for employees, let’s move on to technical measures to reduce the risk of smishing:
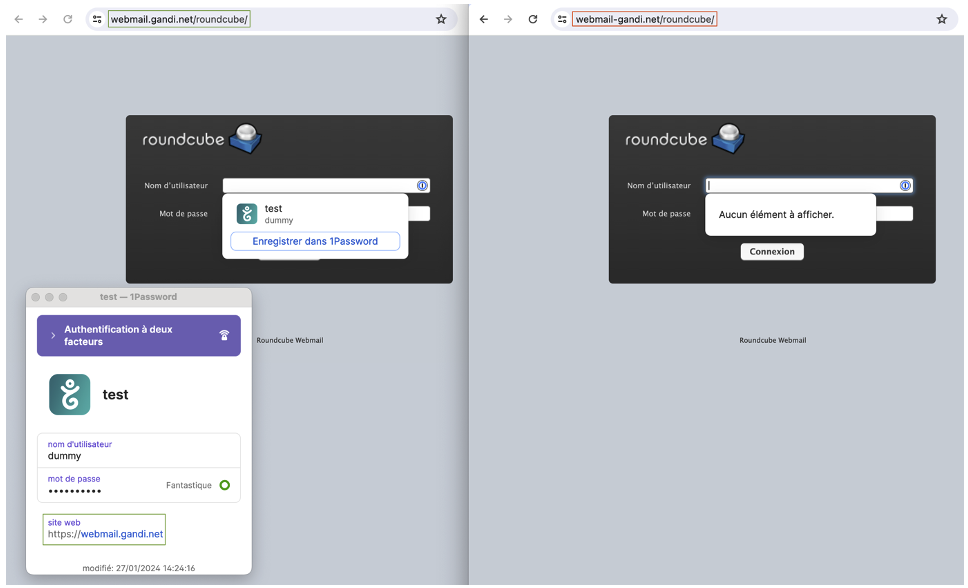
As you can see, the password manager also supports multi-factor authentication (the 2FA code will be generated by 1Password in this case). To talk more specifically about smishing, setting up a password manager on a mobile phone depends on the access you want. It may be preferable for certain applications to be accessible only from a computer.
The distinction between business and personal phones must also be taken into account. It is undesirable for passwords to sensitive applications to be stored on a personal device, which is undoubtedly less secure than a business device.
In conclusion, there are a number of good habits that all employees should adopt in a climate of goodwill. At the same time, technical measures can be taken to limit the risk of smishing and phishing in general.
Author: Benjamin BOUILHAC – Pentester @Vaadata