What is IoT Penetration Testing?
An IoT penetration test assesses the security of a connected device by simulating real-world attack conditions. The tests can cover various aspects, including IoT devices themselves, communication protocols, associated cloud platforms, and the mobile or web applications used to manage them. They focus on identifying vulnerabilities in device configurations, authentication mechanisms, and the security of transmitted and stored data.
At the end of an IoT pentest, our auditors provide a detailed report outlining the vulnerabilities identified, potential exploitation scenarios and remediation recommendations. A validation phase may then be conducted to ensure that fixes have been properly implemented, verify the absence of unintended side effects and produce a final validation report to ensure the security and robustness of the connected device.
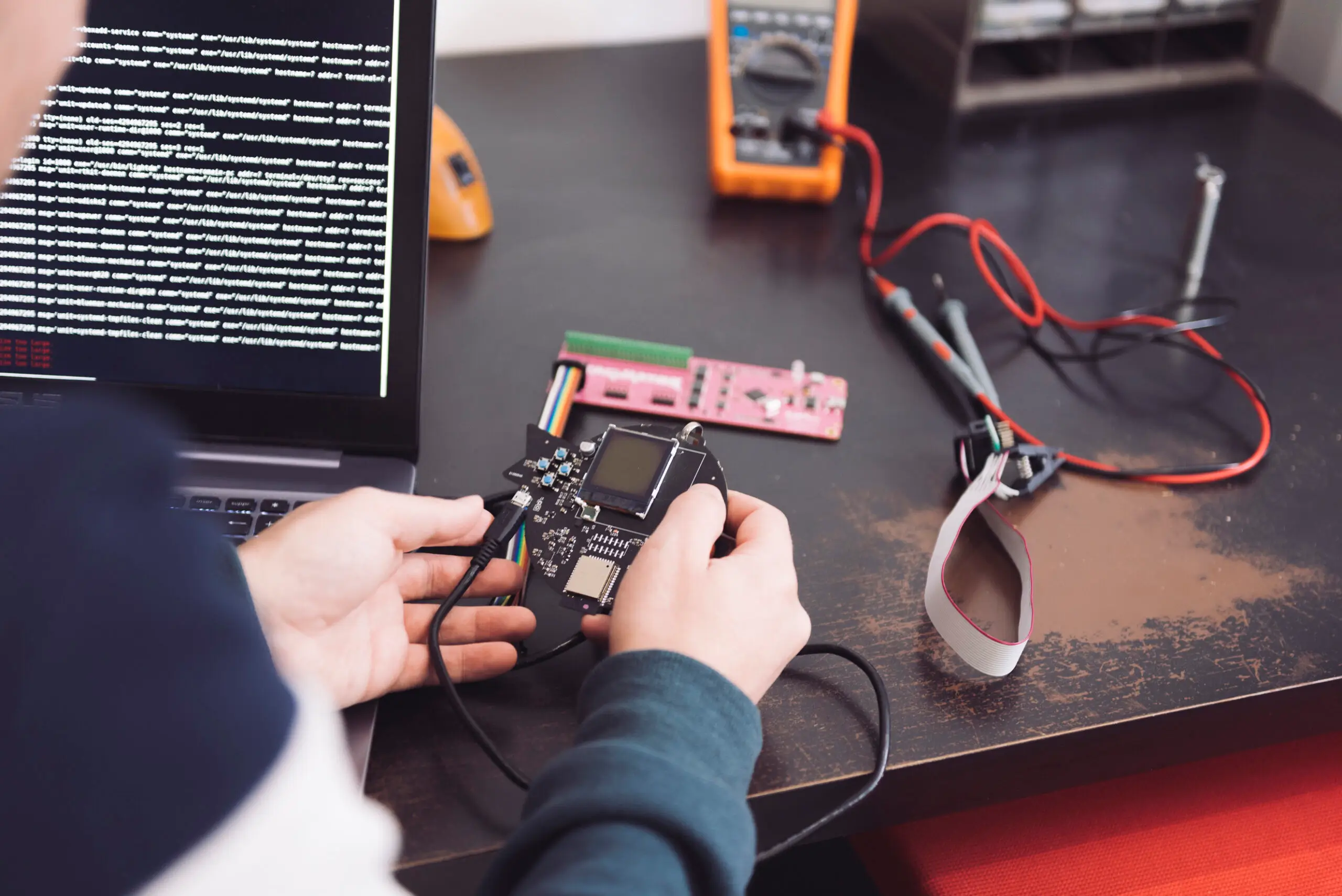
Hardware Penetration Testing
Physical analysis and hardware recon
- Identification of critical components: debug ports, programming interfaces, memory chips, expansion connectors
- Evaluation of physical protections and inspection of the PCB
Assessment of exposed interfaces
- Mapping of exploitable entry points
- Verification of test port activation in production
- Assessment of risks related to PCB routing and board design
- Checking of unauthorised access protections
Access testing via consoles and debug ports
- Connection via UART or JTAG
- Access to debug console and log retrieval
- Initialisation of a system shell
- Direct memory reading and execution of unauthorised commands
Analysis and extraction of embedded memory
- Audit of EEPROM, NAND and NOR chips
- Dumping techniques for content extraction
- Search for identifiers, cryptographic keys and plaintext secrets
- Evaluation of resistance to reverse engineering (obfuscation, anti-tampering protections)
Disruption tests and advanced hardware attacks
- Fault injection, voltage glitching, clock glitching
- Observation of behaviour under abnormal conditions
- Potential bypassing of software protections
- Access to undocumented maintenance modes

Firmware Penetration Testing
Static analysis
- Search for sensitive strings (identifiers, cryptographic keys)
- Detection of vulnerable functions or libraries
- Verification of security configurations and settings
- Inspection of critical sections: authentication, communications, updates
Dynamic analysis
- Identification of execution vulnerabilities (buffer overflow, memory errors)
- Testing update mechanisms to detect malicious code injection
- Observation of behaviour in real or simulated conditions
Audit of integrated security mechanisms
- Verification of firmware integrity control systems
- Detection of backdoors or weak authentication
- Identification of routines allowing unauthorised access
Testing resistance to combined physical and software attacks
- Reverse engineering software and hardware protections
- Manipulating bootloader settings and startup sequences
- Evaluating overall robustness against advanced attacks
Assessment of Communication Protocols
Identification and mapping of protocols used
- Detection of protocols: HTTP/HTTPS, MQTT, CoAP, BLE, ZigBee, LoRa, NB-IoT or proprietary protocols
- Interception and analysis of frames on radio, Wi-Fi, Bluetooth or wired interfaces
Analysis of encryption and authentication
- Verification of the presence and robustness of encryption
- Evaluation of authentication mechanisms and session management
- Detection of vulnerabilities allowing replay attacks, spoofing or packet injection
- Identification of unencrypted or poorly encrypted communications exposing identifiers, passwords or personal data
Specific tests on wireless protocols
- Assessment of resistance to jamming and spoofing
- BLE analysis (services, characteristics) to detect unauthorised access
- Verification of the possibility of sending malicious commands
Audit of critical communications
- Security analysis of exposed REST APIs
- Verification of MQTT configurations and access controls
- Assessment of risks of compromise via unsecured protocols
Assessment of protection against network attacks
- Tests against Man-in-the-Middle (MitM) attacks
- Verification of resistance to frame interception and modification


Audit of Web and Mobile Interfaces
For web applications, our tests are based on OWASP standards (particularly the OWASP Top 10) and seek to detect common flaws such as SQL injections, XSS, poor security configurations, authentication vulnerabilities and data leaks.
For mobile applications, our tests are based on the MASVS (Mobile Application Security Verification Standard). The audit includes a reverse engineering phase of the APK or IPA, analysis of the native code, identification of third-party dependencies, and study of network communications.
Conduct an IoT Penetration Test with Vaadata, a Certified Offensive Security Expert
Choosing Vaadata to perform an IoT pentest means calling on a leading company certified to strict security standards. Vaadata is PASSI, CREST, ISO 27001, and ISO 27701 certified, which guarantees the quality of our tests and their compliance with the most demanding standards in cybersecurity and data protection. These certifications demonstrate our commitment to adopting best practices for information security and our compliance with legal requirements.
Our auditors also hold recognised certifications, attesting to their expertise in identifying and exploiting vulnerabilities in IoT devices. Our IoT penetration testing methodology is based on proven frameworks, ensuring comprehensive coverage of potential vulnerabilities, from configuration errors to flaws in communication protocols, APIs, or management interfaces.
Depending on your specific needs, we can tailor the scope of the IoT penetration test to focus on the most sensitive areas or perform a comprehensive analysis of the entire IoT ecosystem. We offer personalised support and detailed reports to help you strengthen the security of your connected devices while ensuring complete confidentiality.





Our Latest Resources
Ransack Query Injection: Analysis and Exploitation of an ORM Vulnerability