What is Web App Penetration Testing?
A web application penetration test assesses the security of a web application by simulating attacks. Our auditors assess both technical vulnerabilities and logical flaws across functionalities, third-party components and APIs. The hosting environment is also included in the assessment, whether it is based on traditional or cloud infrastructure.
Following the testing phase, our auditors provide a detailed report, including a description of the vulnerabilities identified, exploitation scenarios and recommendations for remediation. A revalidation phase can then be carried out to verify that the fixes have been properly implemented and to ensure the security of your web application.

Our Technical Expertise in Web Application Penetration Testing
Our auditors carry out penetration tests on web applications built using a wide range of languages, frameworks and environments. Whether it is a traditional architecture, a CMS, a microservices architecture, or a complex cloud environment, we adapt our approach to your technical stack.
Tests Performed During a Web Application Penetration Test
Authentication and session management
- Multi-factor authentication (MFA) security
- Assessment of password recovery mechanisms
- Resistance to account takeover and session hijacking attacks
Access control assessment
- Evaluation of server-side privilege and role management
- Detection and exploitation of IDOR vulnerabilities
- Identification of missing or misconfigured access controls
Injections and code execution vulnerabilities
- SQL Injection and Command Injection
- Cross-Site Scripting (XSS)
- Remote Code Execution (RCE)
Business logic vulnerabilities
- Detection of exploitable application inconsistencies
- Bypass of critical validations and workflows
- Bypass of client-side mechanisms
Third-party integration security
- Security of external APIs and integrated services
- Software dependency analysis
- Verification of integration configurations and access rights


API Penetration Testing
Authentication and authorisation mechanisms
- Analysis of authentication methods (JWT, OAuth, API keys)
- Assessment of user rights and role management.
- Authentication bypass testing
Access controls and business logic
- Identification of IDOR vulnerabilities
- Server-side validation analysis
- Business rule bypass testing
Parameter manipulation and fuzzing
- Parameter manipulation in API requests
- Fuzzing of JSON and XML objects and API endpoints
- Identification of mass assignment vulnerabilities
Client-server interactions and response handling
- Verification of sensitive data exposure in responses
- Detection of API misuse and abuse
- Detection of anomalous behaviour
Tests Performed on the Hosting Infrastructure
Cloud environment security
- Cloud configuration assessment
- Identity and access management (IAM) analysis
- Access policy assessment
- Audit of security groups and network rules
Web server security
- Audit of exposed services
- Analysis of system and application configurations
- Patch management assessment
- Audit of security mechanisms

Types of Web App Penetration Tests
A web application penetration test can be carried out using three approaches, each offering a unique perspective on the security of your application.
Black box web penetration testing
Our auditors test your web application from the perspective of an external attacker, without any prior information.
Grey box web penetration testing
In a grey box scenario, our auditors have limited but targeted access to the application: user accounts, documentation, etc.
White box web penetration testing
Our auditors assess the security of your application using extensive information: source code, administrator accounts, documentation, etc.
Web App Penetration Testing Methodology
Passive and active reconnaissance
Our auditors map your attack surface by identifying exposed IP addresses, domains and subdomains, as well as the technologies in use. They also identify potential leaks of sensitive information (source code, compromised credentials, backups or publicly accessible files).
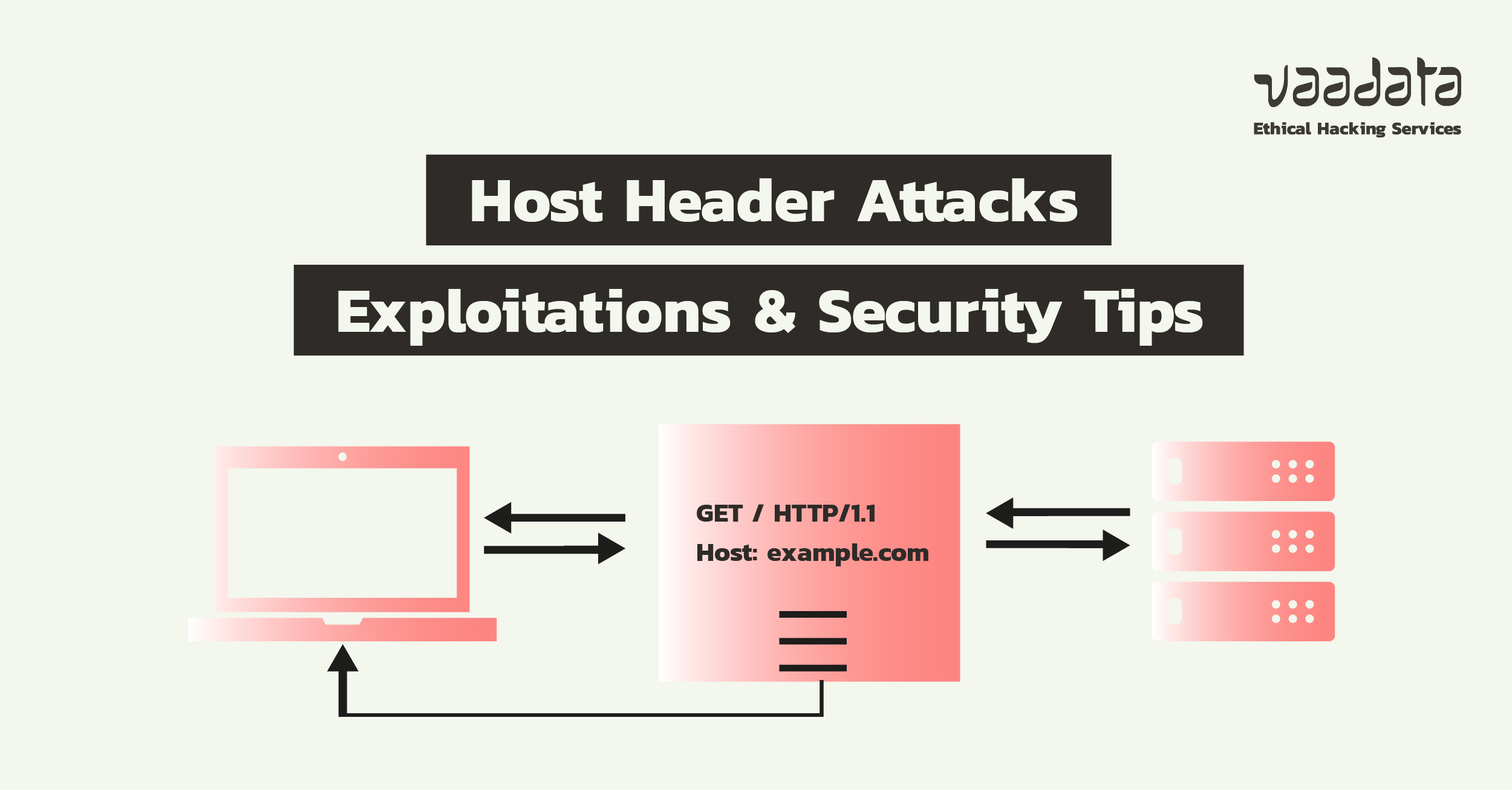
Web application mapping
The application’s architecture and functionality are analysed to identify endpoints, parameters, forms, cookies and HTTP headers. This mapping helps identify potential entry points and attack vectors.
Identification and vulnerability analysis
Vulnerabilities are detected and validated through in-depth manual testing, supplemented by specialised tools. Each vulnerability is assessed based on its severity and real-world impact on your application.
Exploitation and impact assessment
Identified vulnerabilities are exploited in a controlled manner to measure their actual impact, confirm their risk level and identify potential attack chains.
Penetration test report, debriefing and retest
A detailed report outlines the identified vulnerabilities, their severity level, proof of exploitation and prioritised remediation recommendations. A debriefing session with your teams provides an opportunity to walk through the findings and support the remediation process, followed by a retest phase to validate the effectiveness of the measures implemented.

Web Application Penetration Testing with Vaadata, a Trusted Offensive Security Partner
Choosing Vaadata for a web application penetration test means working with a company certified to meet the industry’s most stringent standards.
We are CREST accredited and ISO 27001/27701 and PASSI certified, demonstrating the quality of our services and our compliance with international standards for cybersecurity and personal data protection. These certifications provide our clients with confidence by guaranteeing a high level of methodological and organisational rigour.
Our web application penetration tests are carried out by certified auditors with expertise in advanced attack techniques. Their combined technical and offensive expertise enables them to accurately identify, exploit and document vulnerabilities specific to each application environment.





Our Latest Resources
Ransack Query Injection: Analysis and Exploitation of an ORM Vulnerability