What is Mobile App Penetration Testing?
A mobile application penetration test assesses the security of an iOS or Android application by simulating attacks. The tests cover source code review, the APIs used by the application, application configurations and network communications. They also include identifying vulnerabilities in third-party components, analysing stored data, as well as authentication and session management mechanisms.
Following the assessment, our auditors provide a detailed report outlining the vulnerabilities identified, potential exploitation scenarios and tailored remediation recommendations. A retesting phase can then be carried out to verify that the fixes have been properly implemented and to ensure the security of the mobile application.

Our Technical Expertise in Mobile App Penetration Testing
We carry out comprehensive mobile penetration tests on iOS and Android applications, whether native, hybrid or cross-platform. Our auditors work across a wide range of projects, regardless of the technologies used or the underlying backend infrastructure, to identify exploitable vulnerabilities and strengthen the security of your applications.
MASVS: the Benchmark for Mobile Application Penetration Testing
Our mobile application penetration tests are based on MASVS (OWASP Mobile Application Security Verification Standard), the reference framework for rigorously and systematically assessing the security of iOS and Android applications.
This standard defines a comprehensive framework covering secure development best practices and essential controls to protect data, communications and application logic against real-world attacks. Our tests cover all MASVS categories, including:
- MASVS-STORAGE: Verification of secure storage of sensitive data (PII, tokens, API keys), locally or via system services, to prevent accidental or malicious leaks.
- MASVS-CRYPTO: Analysis of the implementation of cryptographic mechanisms (encryption, key management) to ensure data confidentiality and integrity, even in the event of physical compromise.
- MASVS-AUTH: Review of authentication and authorisation mechanisms (biometrics, MFA, session management) to prevent unauthorised access to user accounts.
- MASVS-NETWORK: Network communication security controls (TLS, certificate pinning, API security) to protect exchanges against interception and MitM attacks.
- MASVS-PLATFORM: Verification of the secure use of mobile OS-specific features (IPC, WebView, notifications, UI) to prevent exposure of sensitive data.
- MASVS-CODE: Assessment of code robustness against untrusted inputs (validation, deserialisation, injection) according to secure development best practices.

Android Penetration Testing
Static analysis of the APK
- Identification of sensitive unencrypted strings
- Detection of code vulnerabilities and hardcoded keys
- Evaluation of authentication mechanisms and access controls
Dynamic analysis and attack simulation
- Interception and modification of traffic via proxy (e.g. Burp Suite)
- Capture and analysis of system logs
- Code injection at runtime via frameworks (e.g. Frida)
Local storage security audit
- Verification of sensitive data in SQLite, SharedPreferences, files, and Keystore
- Inter-app access control
Audit of permissions and exported components
- Detection of excessive or dangerous permissions
- Verification of protection for exported components
- Analysis of risks related to inter-application communications
Resilience tests
- Resistance to traffic interception (TLS/pinning)
- Anti-root protection
- Hooking and code injection tests
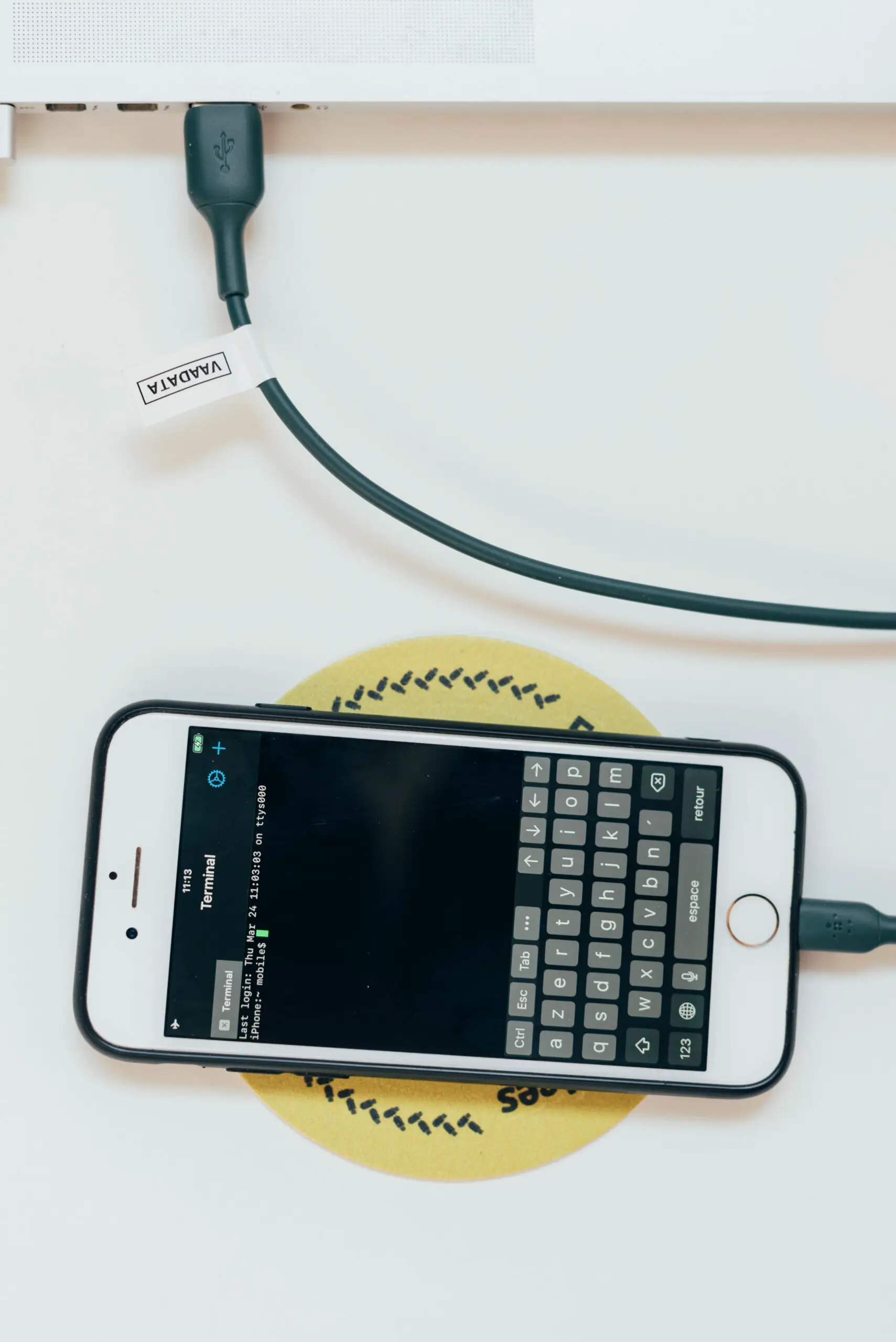
iOS Penetration Testing
Static analysis of the IPA file
- Decompilation of the binary and exploration of the source code
- Search for API keys, hard-coded secrets and sensitive strings
- Evaluation of authentication and access control mechanisms
- Analysis of metadata, permissions requested and frameworks used
Dynamic analysis and attack simulation
- Execution on physical device or instrumented simulator (often jailbroken)
- Observation of behaviours: session management, network communications, access to local storage
Local storage security audit
- Verification of the absence of unencrypted storage of sensitive data
- Checking the contents of storage spaces: sandbox, SQLite databases, plist files and Keychain
API and backend communications audit
- API security testing
- Detection of vulnerabilities: injections, authentication bypasses, privilege escalations
- Simulation of man-in-the-middle attacks to identify potential data leaks
Analysis of anti-reverse engineering and anti-bypass protections
- Resilience testing against: traffic interception, decompilation, hooking, code injection
- Verification of anti-jailbreak protections and potential deactivation of native mechanisms (e.g. Secure Enclave)
Types of Mobile App Penetration Tests
A mobile application pentest can be conducted using three complementary approaches, each offering a different perspective on the security of your iOS or Android application.
Black Box Mobile App Penetration Testing
Black box mobile pentesting involves testing the security of an iOS or Android application without prior access to the source code or internal information.
Grey Box Mobile App Penetration Testing
Mobile grey box pentesting combines an external approach with partial access to internal information (technical documents, test accounts, API keys, etc.).
White Box Mobile App Penetration Testing
White box mobile pentesting relies on full access to source code, technical documentation, the development environment, etc.
Mobile App Penetration Testing Methodology
Reconnaissance and information gathering
Our auditors analyse the APK or IPA to identify key metadata (package, permissions, exposed components) and map the associated backend architecture (APIs, third-party services, servers). This phase includes identifying the technologies used and conducting OSINT research to detect any information leaks.
Static code analysis
Our auditors analyse the code to identify exposed secrets, API keys, tokens, sensitive URLs and poor development practices. We also evaluate the use of critical functions (authentication, encryption, storage), third-party libraries and the effectiveness of protection mechanisms (obfuscation, anti-debugging, excessive permissions).
Dynamic analysis of the application and Webviews
Our auditors assess the actual behaviour of the application on physical or emulated devices. Network exchanges are intercepted and analysed (TLS, certificate pinning), logs are examined, and the application is instrumented to test its resistance to manipulation. Particular attention is paid to local storage and WebViews, which are frequent vectors of exposure.
Reverse engineering and instrumentation
Our auditors perform reverse engineering to analyse the internal logic of the application and bypass its protection mechanisms. We test the bypass of certificate pinning and anti-root/jailbreak controls, instrument critical functions, and examine rights management to identify hidden features, debugging mechanisms, or weak encryption implementations.
Exploitation and post-exploitation
The vulnerabilities identified are exploited in a controlled manner in order to measure their real impact. In particular, we test privilege escalation, identity theft, access to or exfiltration of sensitive data, and the injection of malicious payloads via APIs or WebView. Advanced scenarios can be simulated to assess the technical and business impacts.
Mobile application pentest report
Following the tests, we provide a detailed and actionable report ranking vulnerabilities by criticality, with evidence of exploitation and prioritised remediation recommendations. A post-correction validation phase can be carried out to confirm the effectiveness of the fixes and the final security level of the mobile application.

Mobile Application Penetration Testing with Vaadata, a Trusted Offensive Security Partner
Choosing Vaadata for a mobile app penetration test means working with a company certified to the most stringent international standards: CREST, PASSI, ISO 27001/27701. These certifications guarantee the quality, compliance and rigour of our offensive security audits.
Our auditors hold industry-recognised technical certifications, demonstrating their advanced expertise in analysing vulnerabilities specific to mobile environments (iOS, Android). Their mastery of reverse engineering, network analysis and authentication bypass methods enables them to identify complex flaws often missed by automated testing tools.
Vaadata offers a flexible approach tailored to your priorities: targeted assessments of critical modules or a comprehensive analysis of your mobile application. You benefit from personalised support, concrete recommendations and clear deliverables to enhance your application’s security over time.





Our Latest Resources
Ransack Query Injection: Analysis and Exploitation of an ORM Vulnerability